AES Encryption Function
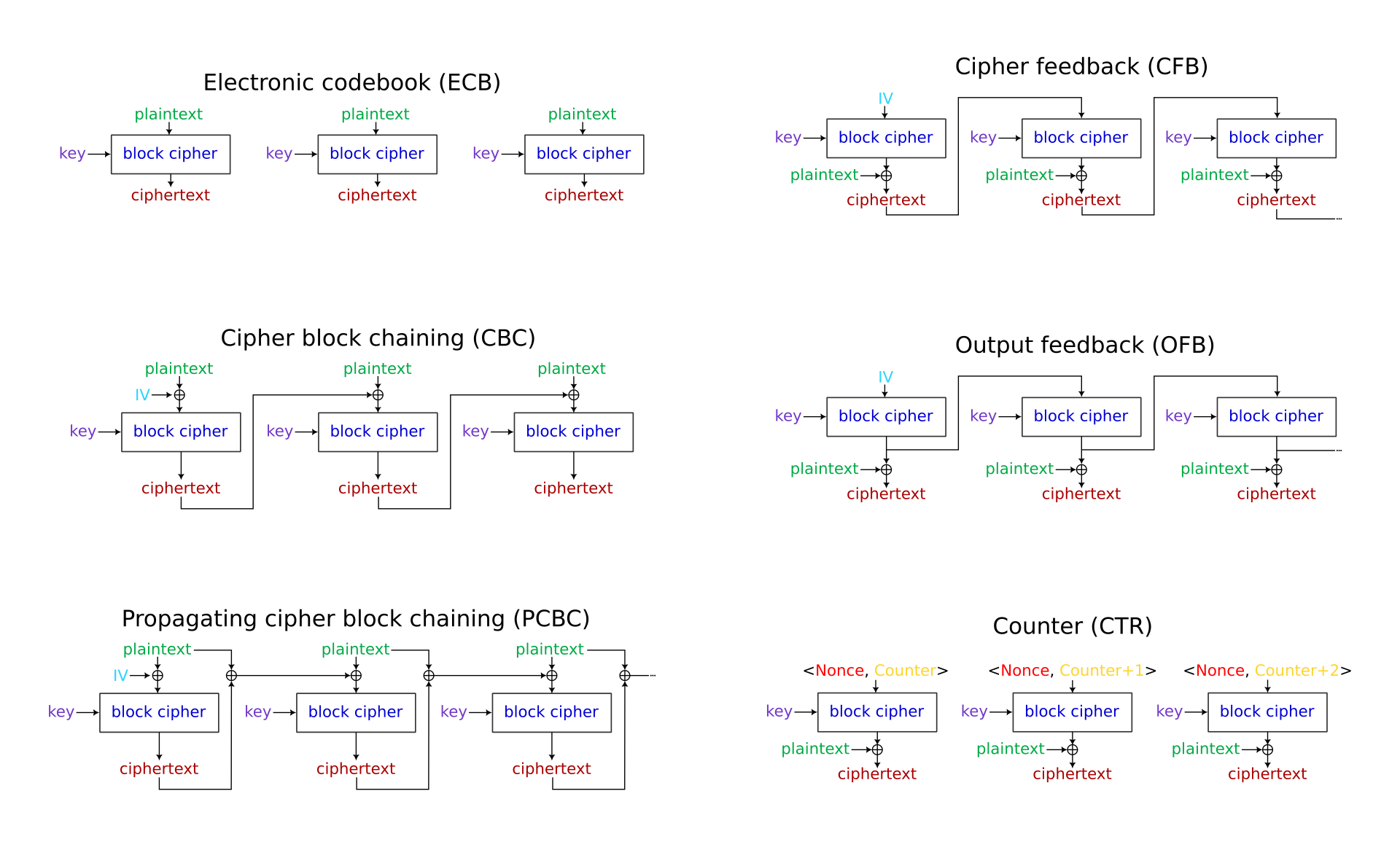
Free online AES encrypt and decrypt tool supporting 128/256 bit encryption online. Includes CBC, ECB, CFB, OFB, and CTR modes, with Hex/Base64 format conversion.
Free online AES encrypt and decrypt tool supporting 128/256 bit encryption online. Includes CBC, ECB, CFB, OFB, and CTR modes, with Hex/Base64 format conversion.
The AES algorithm officially replaced DES as the new generation encryption standard in 2001. This transformation originated from a global algorithm solicitation activity initiated by the National Institute of Standards and Technology (NIST). After rigorous screening, the Rijndael algorithm ultimately prevailed and was established as Federal Information Processing Standard FIPS 197, marking the entry of encryption technology into a new stage of development.
| Mode | Initialization Vector | Parallelism | Error Propagation |
|---|---|---|---|
| CBC | Required | None | Block-level |
| CTR | Counter Initial Value | Supported | No propagation |
| Mode | Standard Document | Padding Scheme | Use Case |
|---|---|---|---|
| PKCS#7 | RFC 5652 | Pad n bytes with value n | General data |
| ZeroPadding | Industry Practice | Pad with 0x00 bytes | Binary data |
| ISO/IEC 7816-4 | ISO Standard | First byte 0x80 followed by 0x00 | Smart card apps |
Advanced Encryption Standard (AES) is a symmetric encryption algorithm established by the U.S. NIST. It uses the same key for both encryption and decryption and is widely considered the global standard for securing sensitive data.
The numbers refer to the length of the encryption key in bits. AES-128 uses a 16-byte key, AES-192 uses a 24-byte key, and AES-256 uses a 32-byte key. AES-256 provides the highest level of security and is often required for military or highly sensitive data.
CBC (Cipher Block Chaining) or CTR (Counter) are the most recommended modes for general use as they provide good security. ECB (Electronic Codebook) is the simplest but least secure mode, as identical plaintext blocks produce identical ciphertext blocks. Avoid ECB unless strictly required.
An IV is a random or pseudo-random value used in conjunction with the secret key to encrypt data. It ensures that encrypting the same plaintext multiple times produces different ciphertexts. Modes like CBC, CFB, and OFB require an IV (usually 16 bytes for AES).